CNAPP
Cloud-Native Application Protection Platform
Uptycs is the top CNAPP choice for security teams collaborating with developers to safeguard critical application pipelines, mitigate risks, and defend runtime environments in the hybrid cloud.
Secure Your Hybrid Cloud from
Dev to Runtime
Modern developers do more than just code; they build and set up cloud infrastructure while actively managing and fixing application vulnerabilities, leading to an expanding code-to-cloud risk.
Uptycs CNAPP helps address this risk by providing the visibility, prioritization, and remediation needed to safeguard applications from development through to runtime.
.png?width=1980&height=1228&name=Evidence%201%20(2).png)
See Risk
Uptycs offers continuous, all-time visibility, correlating telemetry across the hybrid cloud and development pipeline. This enables insights into risks at cloud speed and scale, along with historical data analysis for past events.
Prioritize Risk
Uptycs prioritizes code-to-cloud vulnerabilities and threats by looking at available remediations, asset value, and the latest exploit data from threat intelligence feeds.
Remediate Risk
Uptycs streamlines and guides the remediation of vulnerabilities and threats throughout the software development lifecycle and into production deployment.
Want the technical details?
Streamline, Secure, and Save
Uptycs CNAPP consolidates cloud security silos into a unified platform, providing a single security console, policy framework, and data lake. This unification enables greater automation, simplifies policy enforcement, and extends security coverage, all while reducing costs.
.png?width=1958&height=1218&name=overview%201%20(2).png)
Consolidate
Tools
Uptycs consolidates security tools and siloed data into a single CNAPP, providing one source of truth and rationalizing point solutions for:
- Workload Protection
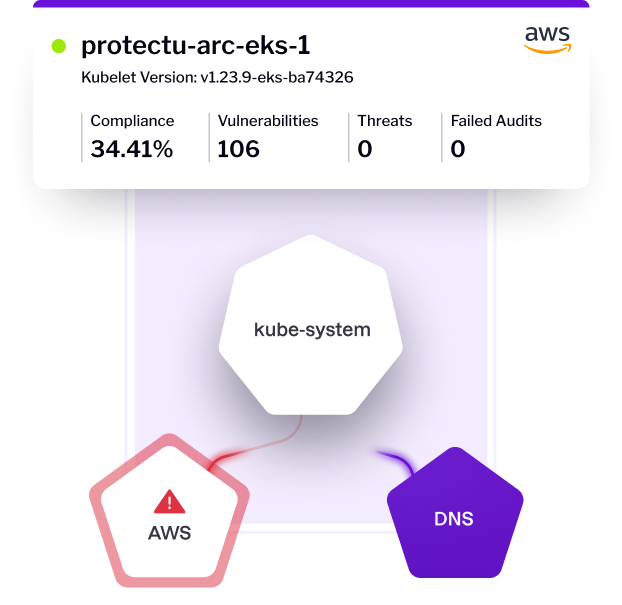
- Container and K8s Security
- Posture Management
- Entitlement Management
- Threat Detection and Response
- Developer Ecosystem Security
Streamline Workflows
Uptycs replaces the need for multiple cloud security tools, consolidating your toolset and streamlining your security workflows. With its single policy framework and data lake, it ensures no alerts are missed, enables real-time correlations, and automates remediations.
Reduce
Costs
By consolidating cloud security tools, Uptycs reduces costs and the time needed to manage multiple contracts and renewals. It also lightens your SecOps teams' workload by minimizing training requirements and streamlining security and compliance workflows.
See What Other CNAPPs Miss
Get the whole picture with real-time and historical visibility
Uptycs uniquely blends real-time and historical data-driven insights across the hybrid cloud and development pipeline, enhancing compliance reporting, vulnerability management, and threat hunting.
.png?width=1986&height=1222&name=Image%201%201%20(2).png)
Compliance Reporting
Audits and reporting are a snap with drill-down dashboards, detailed evidence gathering featuring lookback retrieval, targeted remediation guidance, and out-of-the-box policy templates (SOC2, PCI DSS, CIS Benchmarks, etc).
Feature Spotlight
Uptycs Flight Recorder
Flight Recorder offers a historical lookback for investigation and reporting. It collects and analyzes detailed telemetry, including process, file, and socket events, with a data retention period of 30 or more days, and features Time Machine for specific period playback.
With its capability to investigate workloads no longer running, it's an ideal tool for compliance with the SEC Disclosure Rule and other reporting regulations.
Vulnerability Remediation
Centralize vulnerability management of your development and runtime environments to fix the issues that matter. Uptycs prioritizes insights, delivering automated notifications and guided remediation to streamline management.
Feature Spotlight
Uptycs SDLC Policy Controls
Uptycs secures image deployment across the SDLC with policies that detect secrets, malware, and unresolved vulnerabilities. It consistently applies these rules from CI to runtime and clearly traces failures back to specific policies and image layers for fast fixes.
The system offers flexibility with options for audit notifications or strict enforcement, catering to various development and production workflows.
Threat
Hunting
Accelerate investigations with Security Graph, Attack Path, and Ask Uptycs. These tools help hunters quickly understand relationships between users and assets, and focus investigations with both historical and real-time queries.
Feature Spotlight
Uptycs Security Graph
The Uptycs Security Graph enables security teams to assess the extent of a security breach, such as a compromised developer's laptop.
By rapidly identifying affected cloud assets, whether connected through APIs or SSH, the tool aids in determining the incident's blast radius and guides an effective response strategy.
CNAPP Visibility That Reliably Scales
Your cloud applications scale rapidly, moving at cloud speed. Can your security solution keep pace without disruptions?
Uptycs offers hybrid cloud security with scalability, reliability, and flexibility for real-time telemetry collection, with or without a sensor. The choice is yours. Our scalability is proven, reliably spanning deployments that support millions of workloads.
Deploy in minutes with instant-on, agentless coverage to inventory your cloud infrastructure and assets.
Use the Uptycs Sensor when higher levels of visibility and advanced security capabilities with remediation are required.
Powerful scanning, detection, and remediation tools for the hybrid cloud.
Ready for today and tomorrow
Uptycs is ready for your evolving hybrid cloud, providing deep support for AWS, Azure, Google Cloud, rare Linux distros, IBM AIX, Linux on Z, HPC environments, and more.
Works with What You Have
You rely on an existing suite of tools, and adding a CNAPP shouldn't complicate your team's work. That's why Uptycs works seamlessly with your existing tech stack.
Resources for
the modern defender
Gartner CNAPP Market Guide
![294x230 Gartner CNAPP Market Gui[1]](https://www.uptycs.com/hs-fs/hubfs/294x230%20Gartner%20CNAPP%20Market%20Gui%5B1%5D.png?width=294&height=230&name=294x230%20Gartner%20CNAPP%20Market%20Gui%5B1%5D.png)
Mastering Kubernetes Security
![Mastering Kubernetes Security e-book (2)[2]](https://www.uptycs.com/hs-fs/hubfs/Mastering%20Kubernetes%20Security%20e-book%20(2)%5B2%5D.png?width=300&height=300&name=Mastering%20Kubernetes%20Security%20e-book%20(2)%5B2%5D.png)
Lookout Case Study
![Lookout Quote[1]](https://www.uptycs.com/hs-fs/hubfs/Lookout%20Quote%5B1%5D.png?width=1080&height=1080&name=Lookout%20Quote%5B1%5D.png)
One UI and data model. Multiple solutions.
CLOUD WORKLOAD PROTECTION PLATFORM
Secure your workloads with agentless or agent-based coverage across hosts, VMs, containers, and serverless functions.
Kubernetes Security Posture Management
Identify and fix security and compliance issues within Kubernetes components to prevent supply chain attacks.
Cloud Security Posture Management
Identify and prioritize risks across your cloud environments for a complete picture of your cloud estate.
Cloud Infrastructure Entitlement Management
Protect your cloud resources and infrastructure from unauthorized access, misuse, and insider threat.
Cloud Detection and Response
Detect and respond to threats in the cloud with eBPF based visibility into your entire cloud attack surface.
Dev to prod cloud security
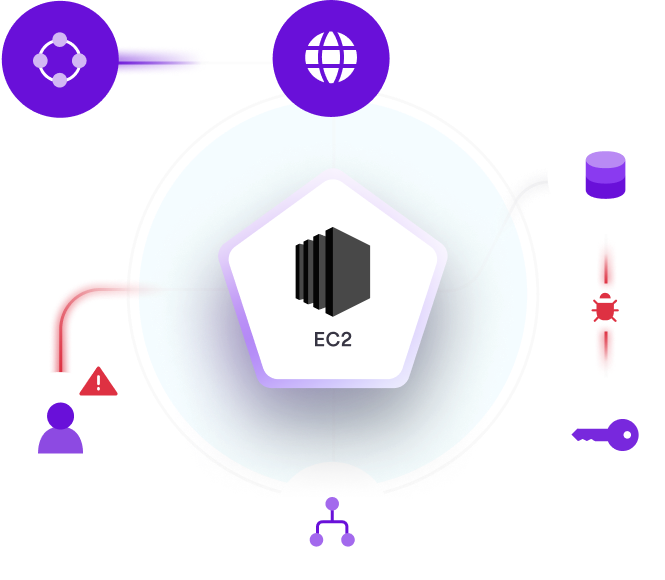
See and stop cloud
threat actors
Detect and respond to attackers anywhere in your environment with visibility into your entire attack surface. With one solution, secure supply chains, infrastructure, containers, hosts, and laptops.
Gain visibility and prove compliance
Shift left to gain unified visibility across your entire cloud estate and prove compliance. Prevent cloud breaches by monitoring and fixing misconfigurations, advancing identity security, and enforcing security policies.

Why industry leaders
choose Uptycs
“Uptycs was deployed on a large scale as a key component of our security posture.”
Comcast
Vice President IT Security“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs has been instrumental for our FedRamp authorization and ISO 27001 certification.”
Grant Kahn
Director, Security Engineering Lookout“Uptycs helps me sleep better at night.”
Sean Todd
CISO Pay Near Me“Uptycs contextualizes threat activity across K8s, cloud services, and laptops. We've dramatically shortened our threat investigation time.”
Anwar Reddick
Director of Information Security Greenlight Financial“Uptycs provides us with a comprehensive view of our environment without the need for log shipping or other data collection methods.”
Cloud Security Engineer
Top 10 Internet Site“I would not want to do security anywhere without this level of visibility.”
Steve Shedlock
Incident Response Team Lead SEI“Everything you want to know is as easy as querying a database. It’s fantastic.”
Security Engineer
E-learning Company“Product works great, is inexpensive, zero Dev complaints about slowing down systems (IYKYK), and they've added every feature I've asked for.”
Security Operations Manager
Business Services Company"Clean interface, very good visibility across assets, and their team is open to feedback."
Manager, Information Security
Finance Industry"A unified view from which we can quickly ask and answer security questions across our environment."
Chris Castaldo
CISO Crossbeam“A major game changer for heavily used hosts (40k requsts per second). Running safely within one of the largest cloud environments on the internet. ”
Uptycs Customer
"Uptycs simplifies investigations and saves time—about 30% per investigation.
Sean McElroy
CSO Lumin Digital“If threat actors try to evade detection Uptycs captures those events”
Security Engineer
Large Telecom Company“Blazingly fast. 0.7 seconds from execution to detection, and 1.6 seconds from execution to case management alert.”
Security Engineer
Global Payment ProcessorUptycs provides actionable runtime threat and vulnerability insights and a flexible threat hunting capability.
Uptycs Customer
Director, Information Security Financial“Monitoring containers for Exploit/Mining Activity can be easily traced compared to other apps”
Security Engineer
Telecom Company“For so many issues, our answer is ‘Go to Uptycs.’”
Director of Security Operations
Enterprise Logistics Company“Uptycs enables us to make risk-based decisions.”
Chris Castaldo
CISO, Crossbeam“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs was deployed on a large scale as a key component of our security posture.”
Comcast
Vice President IT Security“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs has been instrumental for our FedRamp authorization and ISO 27001 certification.”
Grant Kahn
Director, Security Engineering Lookout“Uptycs helps me sleep better at night.”
Sean Todd
CISO Pay Near Me“Uptycs contextualizes threat activity across K8s, cloud services, and laptops. We've dramatically shortened our threat investigation time.”
Anwar Reddick
Director of Information Security Greenlight Financial“Uptycs provides us with a comprehensive view of our environment without the need for log shipping or other data collection methods.”
Cloud Security Engineer
Top 10 Internet Site“I would not want to do security anywhere without this level of visibility.”
Steve Shedlock
Incident Response Team Lead SEI“Everything you want to know is as easy as querying a database. It’s fantastic.”
Security Engineer
E-learning Company“Product works great, is inexpensive, zero Dev complaints about slowing down systems (IYKYK), and they've added every feature I've asked for.”
Security Operations Manager
Business Services Company"Clean interface, very good visibility across assets, and their team is open to feedback."
Manager, Information Security
Finance Industry"A unified view from which we can quickly ask and answer security questions across our environment."
Chris Castaldo
CISO Crossbeam“A major game changer for heavily used hosts (40k requsts per second). Running safely within one of the largest cloud environments on the internet. ”
Uptycs Customer
"Uptycs simplifies investigations and saves time—about 30% per investigation.
Sean McElroy
CSO Lumin Digital“If threat actors try to evade detection Uptycs captures those events”
Security Engineer
Large Telecom Company“Blazingly fast. 0.7 seconds from execution to detection, and 1.6 seconds from execution to case management alert.”
Security Engineer
Global Payment ProcessorUptycs provides actionable runtime threat and vulnerability insights and a flexible threat hunting capability.
Uptycs Customer
Director, Information Security Financial“Monitoring containers for Exploit/Mining Activity can be easily traced compared to other apps”
Security Engineer
Telecom Company“For so many issues, our answer is ‘Go to Uptycs.’”
Director of Security Operations
Enterprise Logistics Company“Uptycs enables us to make risk-based decisions.”
Chris Castaldo
CISO, Crossbeam“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large EnterpriseResources for
the modern defender
Gartner® CNAPP Market Guide
ESG Report: Secure the Expanding Cloud-native Attack Surface
Detecting the Silent Threat: 'Stealers are Organization Killers'

See Uptycs in action
Find and remove critical risks in your modern attack surface - cloud, containers, and endpoints - all from a single UI and data model. Let our team of experts show you how.
